Platforms for PCVE: A Look at the Influencers Countering Islamist Extremism on TikTok
Popular social media platforms have become central to Islamists’ ability to reach mainstream audiences, particularly...
Ecofascist and Nihilistic Extremism: Taking Stock of Evolving Grievances in Targeted Violence Manifestos
When extreme right lone actor terrorists expressed environmental concerns in the manifestos related to attacks...
The Darkest Shade of Green: Strategic Weaponisation of Environmental Governance by Violent Extremist Organisations
Over the last few years, a clear and troubling pattern has crystallised: where the state...
Speed Over Safeguards? The e-Evidence Regulation and Counter-Terrorism Investigations
In March 2026, Europol coordinated its largest-ever referral action targeting terrorist audio propaganda, referring over...
Beyond the Clan: Identity Formation, Influence, and Extremist Milieux in Online Gaming-Adjacent Spaces
Over the past two decades, gaming environments have become increasingly social and massified. Multiplayer games...
Jedag Jedug Jihadists: How TikTok Edits Turn Glorification of Jemaah Islamiyah Figures into Entertainment
On Indonesian TikTok, figures associated with past Jemaah Islamiyah (JI) terrorist attacks are quietly reentering...
The Resurgence of The Base in Europe: The Spanish Cell and a Transnational Accelerationist Network
Introduction In December 2025, Spanish authorities dismantled a cell linked to The Base, an accelerationist...
Francoism Online: Neo-Fascism, Memes, and Historical Revisionism in Spain
In Spain, a recent study indicates that young men are showing an inclination toward far-right...
Propaganda as Financial Infrastructure: How Islamic State and al-Qaeda Media Ecosystems Enable Terrorist Finance
Propaganda ecosystems function as parallel trust infrastructures, enabling extremist organisations to coordinate financial activity outside...
Operation Herof-2: BLA Propaganda, Female Fighters, and Virality on TikTok
On 31 January 2026, the Baloch Liberation Army (BLA) launched a wave of large-scale coordinated...
Operation Ghost Protocol: Infrastructure-Level Evasion in Islamic State Supporter Ecosystems
In a pro–Islamic State Rocket.Chat (TechHaven) channel, a lengthy post appeared on 11 February 2026...
“No shadowbans. No algorithmic games”: The Exploitation of UpScrolled by the pro-Islamic State Online Ecosystem
Major social media platforms have intensified content moderation efforts in recent years in response to...
Rapid Growth, Emerging Risks: Far Right Violent Extremist Content on UpScrolled
By the end of January 2026, the new social media platform UpScrolled became the most...
Al-Qaeda’s Cyber Jihad Movement: Plugging into Iran’s Wartime Hacktivist Ecosystem
On 4 March 2026, the Cyber Jihad Movement (CJM) issued a communiqué on its official...
Understanding Terrorist Innovation: A Case Study in Drone Adoption
Modern conflict has been shaped by the use of new and emerging technologies. The use...
The Designation of 764 Network: Why Does it Matter?
The 764 network is an international online sadistic network which operates at the intersection of...
Operation Herof-2: How Hakkal Media Weaponised the BLA’s Narrative Online
On 31 January, the Baloch Liberation Army (BLA), a designated Foreign Terrorist Organisation, launched the...
Inside the Discord Server: Echo Chambers and the Spread of Gen-Z Radicalisation
This Insight examines how extremist aesthetics and narratives inspired by jihadist groups are produced, circulated,...
AI-led Content Moderation Tools: Are They The Answer To Combatting Online Extremism in Canada?
Social media has proven to be a significant medium fomenting violent extremism, the circulation and...
From Generative AI to Crypto Exchanges: The Infrastructure Behind the GOYIM Token
On 1 February 2026, a meme token called GOYIM appeared on the Solana blockchain, a...
Spain’s New Neo-Nazi Networks: ‘Remigration’ and Radicalisation Online
In Spain, hostility toward immigrants is one of the most prevalent forms of online hate,...
Silent Recruitment: Extremist Child Targeting on Messaging Platforms in Indonesia
In November 2025, Indonesia’s National Police Detachment 88 (Densus 88 AT Polri), together with the...
An ‘Ode to Violence’: Extremist Exploitation of Viggle AI
New and unique online platforms are seemingly constantly cropping up, often ripe for extremist exploitation...
Extremist Nasheeds: Emerging Subcultures and the Cultivation of Radical Online Communities in Southeast Asia
This Insight relies on open-source intelligence to examine how nasheeds – Islamic hymns – are...
Undermoderated and Overlooked: Arabic Online Content on the Bondi Beach Attack
Following the heinous attack on members of the Jewish community celebrating Chanukkah on Bondi Beach...
Warning Behaviours for Right-Wing Violent Radicalisation on Online Platforms: Conceptual Challenges and Empirical Findings
This Insight draws on data from the RadiGaMe project and is funded by the German...
Group Dynamics in Far-Right Telegram Communities: A (Worthy) Challenge for Radicalisation Research
This Insight draws on data from the RadiGaMe project and is funded by the German...
Extremist Content Curation: Moderation Challenges on Pinterest and Means to Move Forward
On 17 October 2025, the Coimisiún na Meán – Ireland’s agency for developing and regulating...
From Confusion to Extremism: How Deepfakes Facilitate Radicalisation
On 14 December 2025, two gunmen opened fire on a public Hanukkah celebration attended by...
Telegram Stars: Exploring Micropayment Exploitation, Digital Goods and the Evolving Tactics of Terrorist Financing
Over the past decade, terrorist organisations have repeatedly demonstrated their ability to adapt to disruption...
Shock and Awe: Geopolitical Disruption and Terrorist Narrative Opportunism Online
The US capture of Venezuelan President Nicolás Maduro and his wife, Cilia Flores, generated a...
Escape The Void: Responding to Youth-Led Nihilistic Violence
This Insight was published as part of GIFCT’s Working Group on Addressing Youth Radicalization and Mobilization...
“Agentic Smurfing”: How AI-Autonomous Micro-Laundering is Outpacing Traditional Terrorist Financing Detection
The convergence of artificial intelligence and cryptocurrency has created a new threat to counter-terrorism financing...
The Moscow Oblast School Stabbing: Digital Rehearsal, Gaming Communities, and Youth Pathways to Violence
In the morning on 16 December 2025, local police were called to a school in...
From Defence to Offence: How Anti-Drone Technologies Are Empowering Militants in a New Era of Coordinated Drone Warfare
In 2025, Pakistani security forces witnessed at least 405 quadcopter attacks by Islamists Tehreek-e-Taliban (TTP)...
3D-Printed Warfare: A New Phase in Jihadist “Do-It-Yourself” Innovation Targeting the West?
This Insight analyses potential security threats associated with the use of 3D-printing technologies for the...
The Moscow Oblast School Stabbing: Understanding Hybrid Radicalisation and Transnational Online Subcultures
The fatal stabbing of a 10-year-old Tajik immigrant schoolboy in the Odintsovo district of Moscow...
Testing Resilience: Can the Proposed EU Drone Wall Defend Against Extremist Actors?
The European Union is developing a “Drone Wall”, officially named the European Drone Defence Initiative,...
Understanding Cyberhacktivist Radicalisation: A Socio-Psychological Approach
Note: The following Insight draws on research conducted by Sonja Belkin and Kristy Sakano under...
The Exploration of Dialogue-Based AI Interventions in P/CVE: Opportunities, Limits, and Lessons
Across the Preventing and Countering Violent Extremism (P/CVE) field, practitioners know that radicalisation processes increasingly...
Modern Warfare: The Islamic State’s Emerging Drone Instruction Ecosystem
Over the past decade, Islamic State (IS) has repeatedly adjusted the way it teaches technical...
The Jakarta Bombing: Youth Digital Radicalisation and the Urgent Need for Adaptive PCVE Responses
This Insight analyses the digital influences, memetic behaviours, and visual-symbolic cues that underpinned the explosion...
The Nordic Front of ‘764’: Trends, Drivers, and Countering Youth Exploitation and Radicalisation
This Insight was published as part of GIFCT’s Working Group on Addressing Youth Radicalization and...
Cutting a Hydra’s Head: Infrastructure-Level Content Moderation and the Case of Kiwi Farms
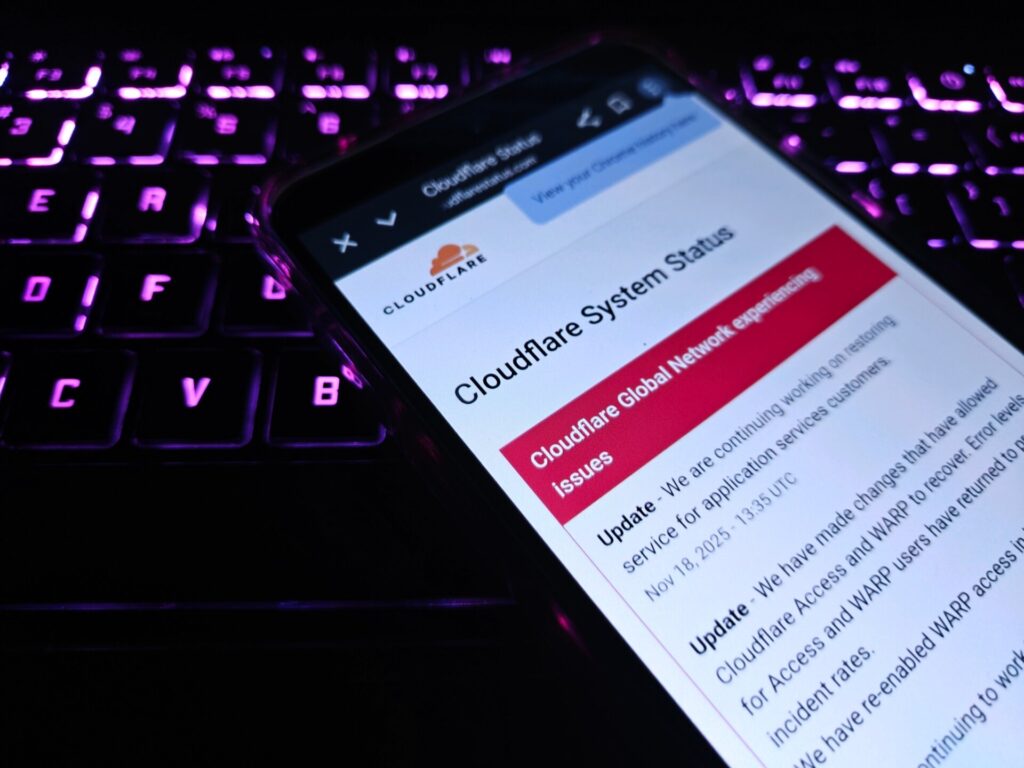
On 18 November 2025, the popular Content Delivery Network (CDN) and Distributed Denial of Service...
Cosplaying Columbine: How Memetic Violence Transformed Southeast Asia’s Extremist Threat
The 7 November 2025 attack at Sekolah Menengah Atas Negeri 72 (SMAN 72) in North...
Participatory Memetic Violence: Legend, Ostension, and Ideologically Diffuse Violence
Folk studies are not a source of analysis often used in the P/CVE space. However,...
Monetising Misogyny: Engagement Farming and the Tactics Behind Incendiary Online Content
This Insight is part of GNET’s Gender and Online Violent Extremism series, aligning with the...
Digital Weaponisation: Taliban Propaganda and Narrative Warfare on X
The Pakistani state and Afghan Taliban forces recently clashed along the Durand Line—one of the...